Enabling Log Collection and Replacing Certificates in VCF Operations for Logs
In the previous post, I deployed a VCF Operations for Logs appliance, but initial configuration still needs to completed.
In this post, I will first enable Log Collection and then replace self-signed certificate with a CA-signed certificate.
To use VCF Operations for logs, you must integrate it with a vCenter instance of version 9 that is licensed with a VMware vSphere Foundation or a VMware Cloud Foundation. By default, the vCenter adapter for VCF Operations for Logs is not enabled, which is why no logs were visible in the previous post after deployment.
The adapter must be manually activated before logs can be collected.
Log into your VCF Operation as admin local.
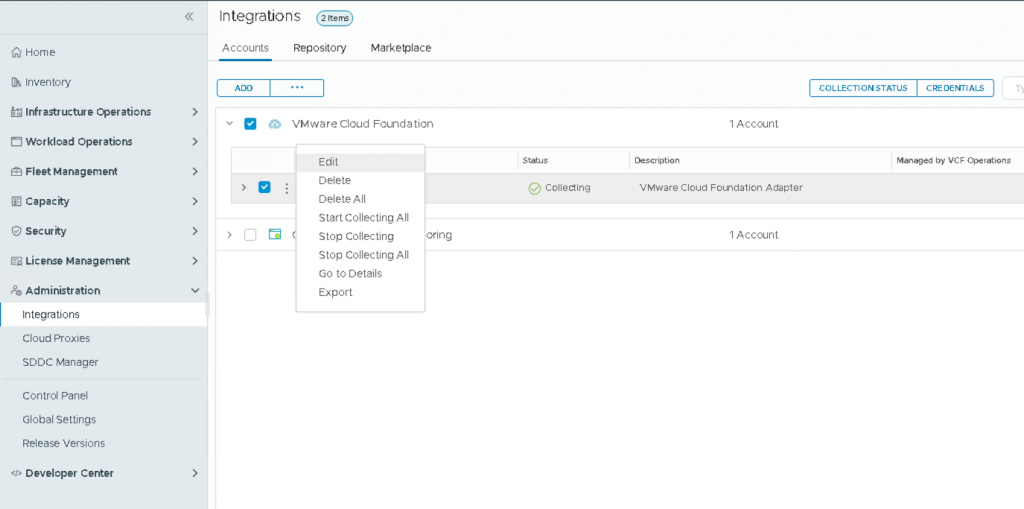
In the navigation pane on the left, click Administration, then Integration. On the Accounts tab, select your vCenter (for example vCenter for Management Domain). Open the three-dot menu, then click Edit to modify VCF adapter settings.
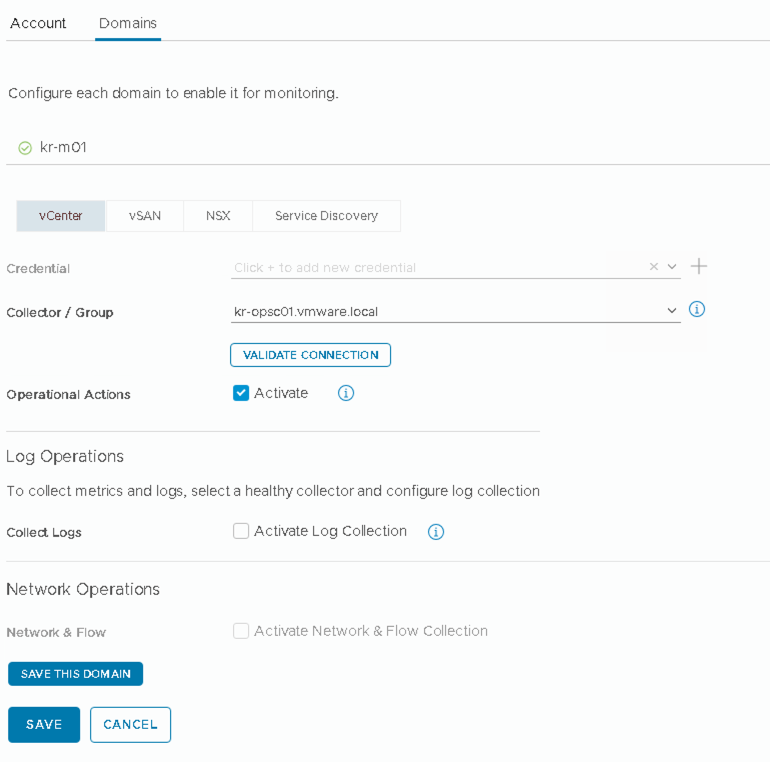
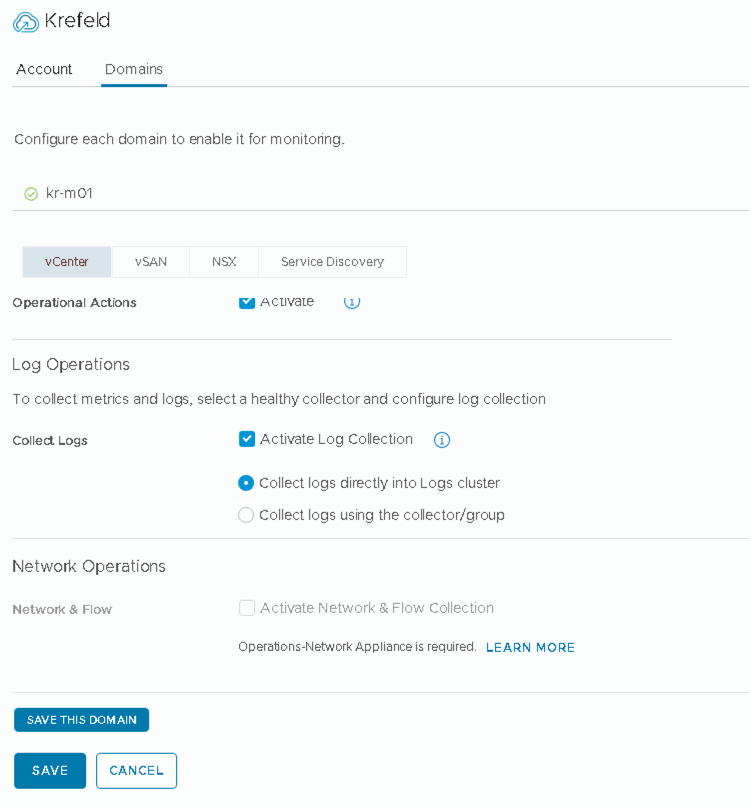
Click Domains tab and then select Activate Log Collection.
When you choose Action Log Collection, two options appear:
- Collect logs directly into logs cluster
- Collect logs using the collector/group
According to VMware Documentation, at least one vCenter integration must be configured to collect logs directly, rather than using a collector or a collector group. The reason is the related to licensing:
To ensure the required license is recognized and applied, you must ensure that at least one vCenter with the appropriate license is configured for direct log collection.
When the vCenter log collection is configured using a collector (Cloud Proxy) or collector group, VCF Operations for logs does not receive an entitlement from the vCenter.
So select Collect logs directly into logs cluster and then Save the configuration.
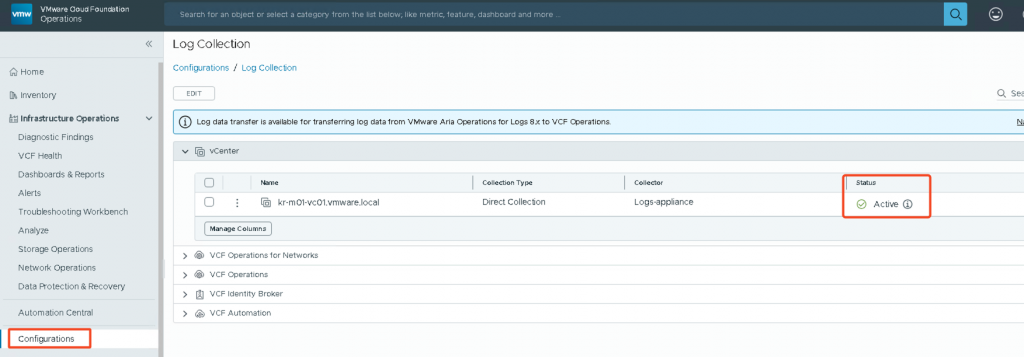
Now if you navigate to Infrastructure Operations, Configurations then Log Collections, you should see the Log Collection status for vCenter marked as Active.
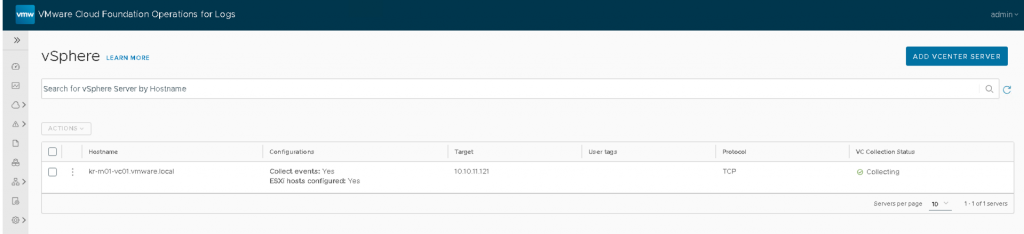
If you log in to VCF Operations for Logs, you will see that vCenter and ESXi integrations are successfully configured and operational.
Now I did my first Day 2 operation task, the next is to replace the default self-signed certificate with a CA-signed certificate.
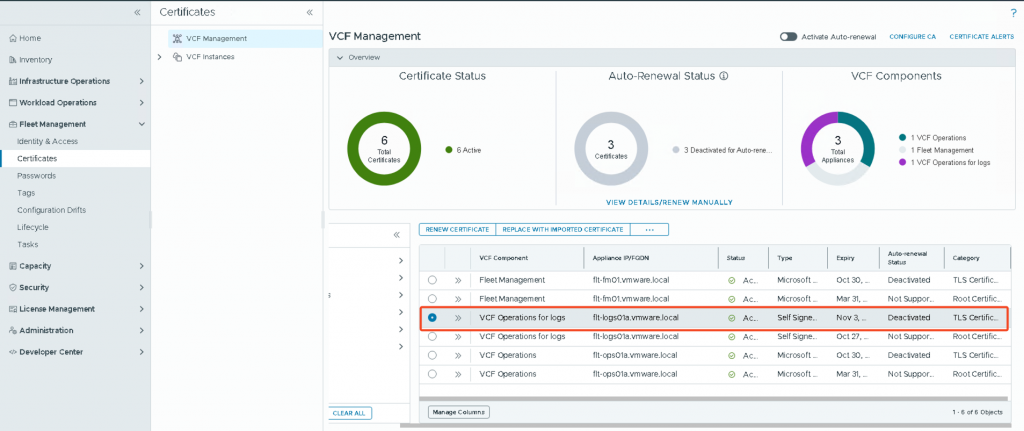
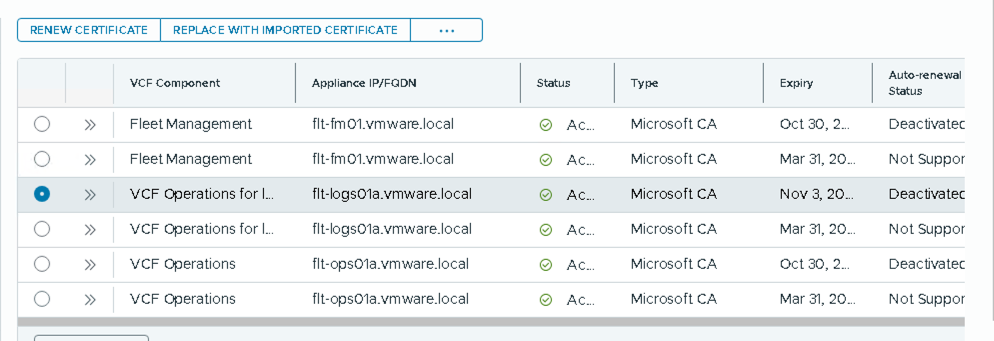
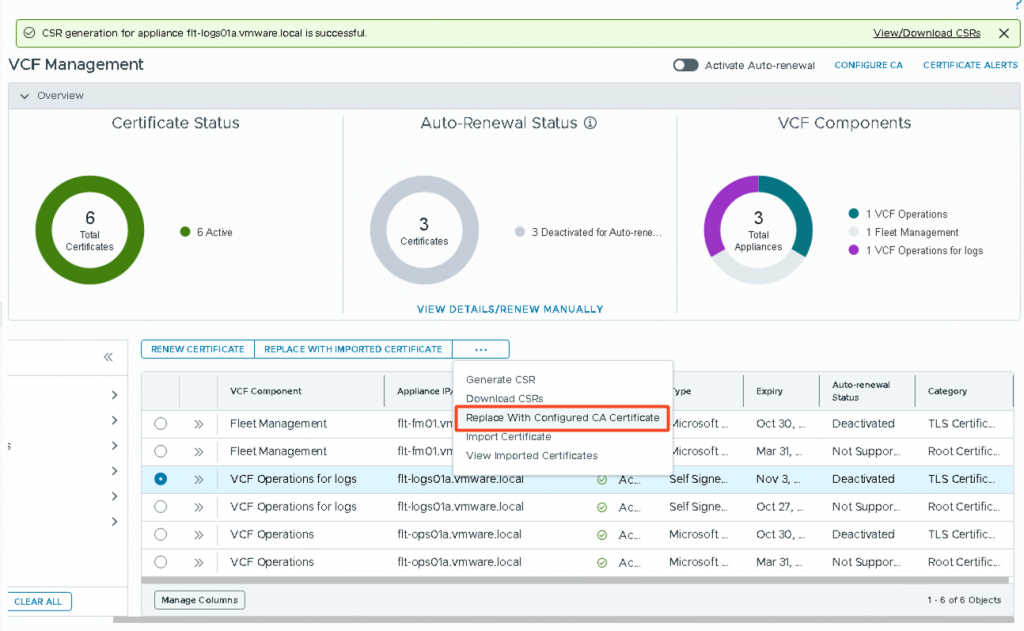
From the navigation pane in VCF Operations, click Fleet Management, then Certificates, then select VCF Management.
From the list of certificates, locate the one for VCF Operations for Logs.
Do not replace the root certificate.
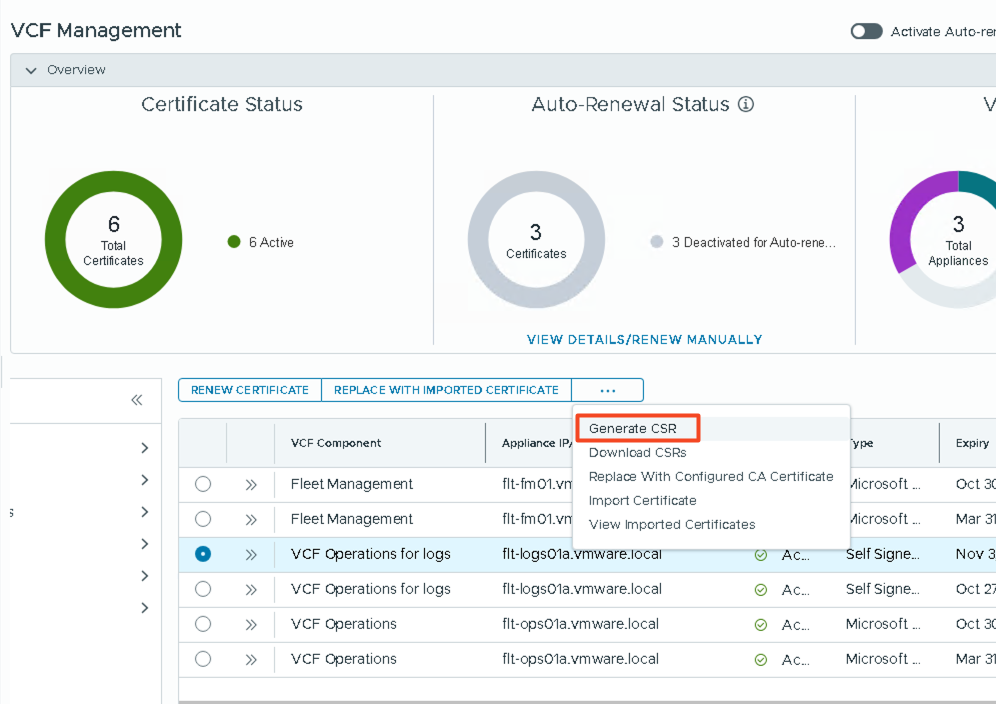
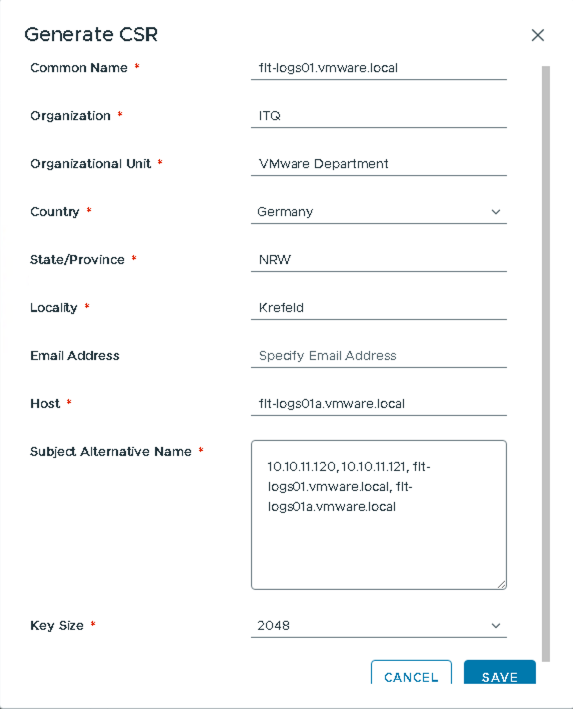
Select the correct certificate and then click Generate CSR from the three-dot menu.
Enter the required CSR details and click Save.
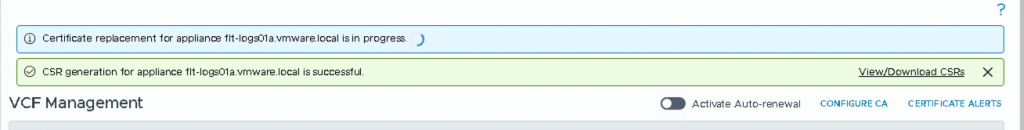
Wait until the CSR is successfully generated. Again, open the three-dot menu and select Replace With Configured CA Certificate.
Confirm certificate replacement.
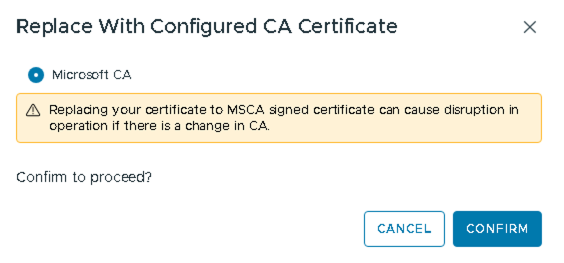
The replacement process usually takes 2–3 minutes. After the certificate is applied, it may take a little time before the updated configuration appears in the UI.
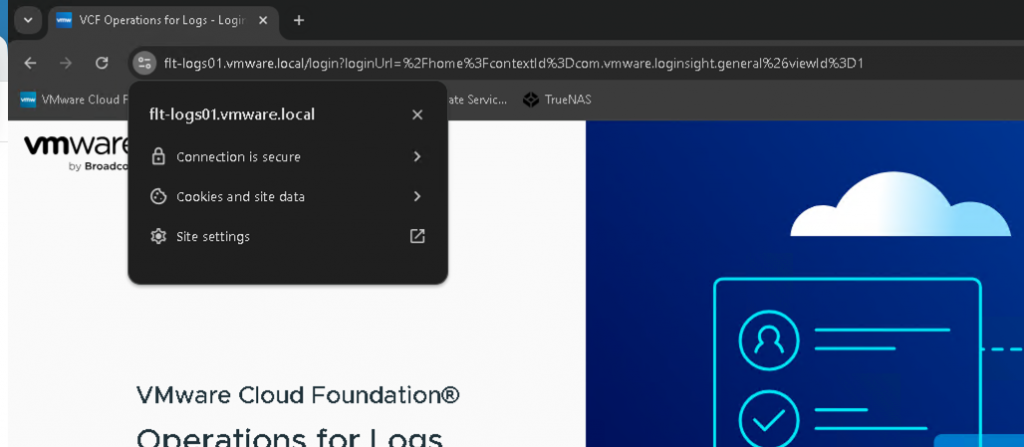
Once complete, your connection should now be secure.
If you check under Certificates, you’ll see the type changed to Microsoft CA, including for the root certificate.
My three take away for production environment:
- For VCF Operations clusters, the certificate must include the FQDNs of all cluster nodes in the SAN (Subject Alternative Name) field.
- If you plan to scale out the cluster by adding additional nodes, update the certificate before scaling, ensuring it includes the new node’s FQDN in the SAN field.
- If using an external load balancer in the HA model, its FQDN must also be included in the SAN field.